From Ghibli trend to Attention Economy, Madhavi Divan addresses growing concerns at release of ‘Informational Privacy: Constitutional and Common Law Remedies’
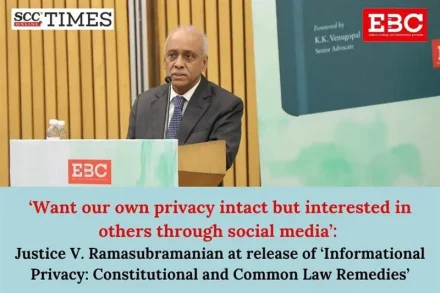
EBC celebrated the release of ‘Informational Privacy: Constitutional and Common Law Remedies’ by Nina Rohinton Nariman, with Justice (Retd.) V. Ramasubramanian, as Chief Guest and Sr. Adv. Madhavi Goradia Divan as Guest of Honour.